- Market-Inspector.co.uk
- Blog
- IoT Security in Smart Office
Security of IoT in the Smart Office

How to Optimise Your Smart Office Security
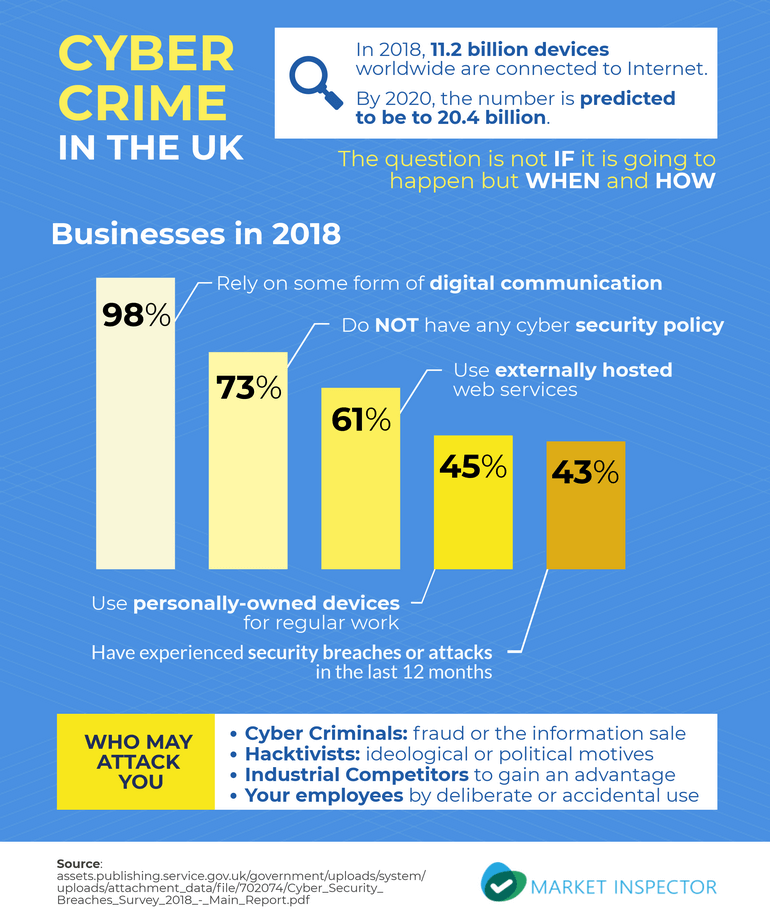
In 2018, 11.2 billion devices worldwide are connected to the internet so far, and it is predicted that by 2020, a staggering 20.4 billion devices will be connected.
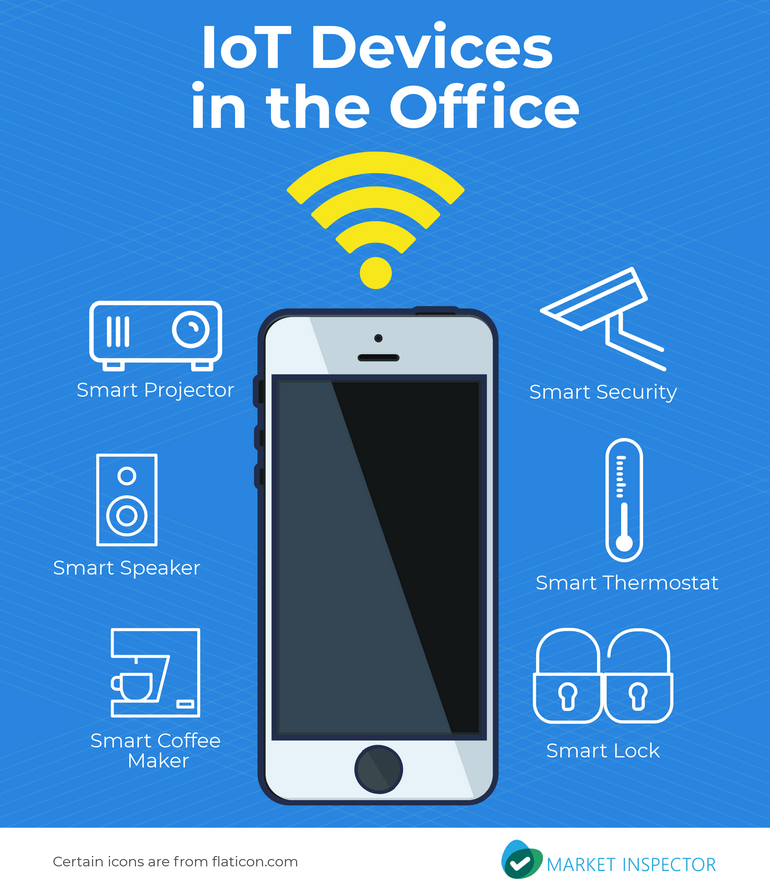
IoT (Internet of Things), has been introduced into our homes and offices for some time now. Plenty of homes are now ‘smart’, with devices such as Amazon Echo, smart locks, coffee machines, robot vacuums, and more. Everyday objects are now able to be connected to the internet, and the use of IoT is ever expanding.
IoT is now making its way into the workplace at a faster rate, with businesses wanting to optimise their smart office. A ‘smart office’ consists of connected devices that monitor, control, and manage various aspects of an office.
Smart devices in the office can increase productivity, add ease to ordinary tasks, and create a comfortable environment for employees. There are devices that control the office infrastructure such as control doors, heating, ventilation, and lighting. There are also devices such as smart speakers, photocopiers, cameras, locks, weather stations, and motion sensors. Here, Market Inspector gives the best examples of IoT devices for the office.
If you would like to use this infographic on your website, use the embed code below:
The Rate of Cyber Crime in the UK
According to the Cyber Security Breaches Survey 2018, 98% of UK businesses rely on some form of digital communications or services. In the UK, 61% of businesses use externally hosted web services to host websites, emails, or transfer or store data. There are also 45% of businesses have staff using their own personal devices for regular work.
Bearing this in mind, concerns about security are increasing for businesses. It is now more imperative than ever that businesses understand the importance and the significance of cyber security and how they can stay secure and prevent any future risks.
Breaches have been found to most likely happen to businesses that possess personal data, where staff use their own personal devices for work, also known as BYOD (bringing your own device).
43% of businesses have experienced cyber security breaches or attacks in the last 12 months. However whilst this is the case, a vast 73% of businesses do not have any cyber security policy or policies.
Potential security risks are prevalent with smart devices being difficult to manage in the office environment due to their different standards. Devices can have basic security protocols, making access easy to vast amounts of data. Microphones, cameras, and devices that record location can open up a window to all types of industrial espionage and an open WiFi network can allow for an outsider to access your business network.
Being a small or a large business doesn’t have any bearing on whether you can be a victim of cyber crime. This is who may want to attack your business:
If you would like to use this infographic on your website, use the embed code below:
Guide to Security for Your Smart Office
The IOTs you may be using in your office may be unknowingly allowing access to cyber criminals. These are the tips that can add an extra layer of security to your IOT setup.
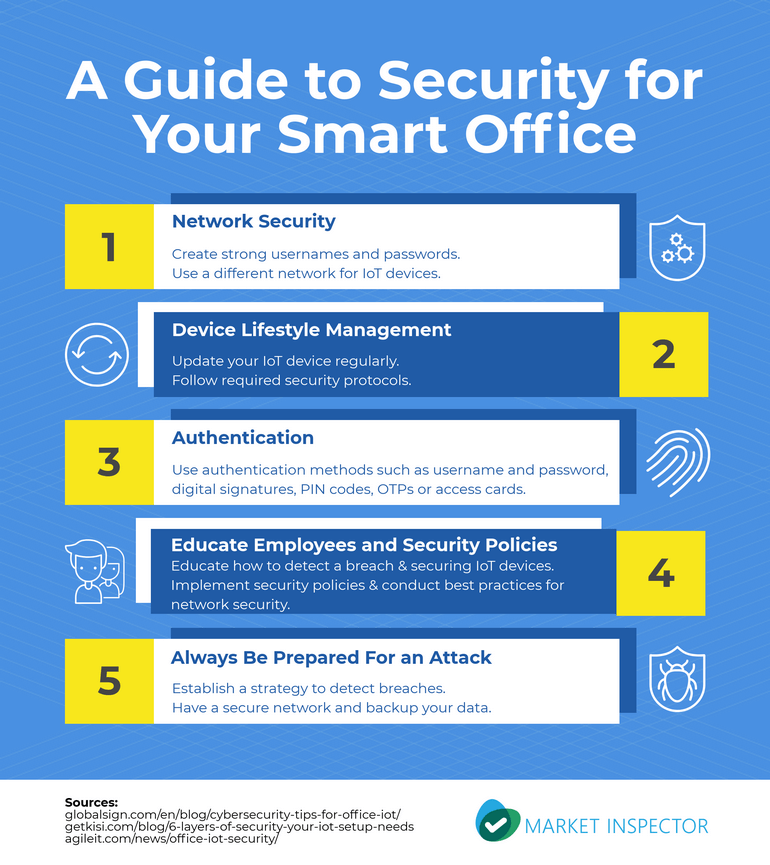
Network Security
Most IoT devices are wireless and therefore can be challenging to secure. There are different device operating systems and standards, but one of the easiest ways to secure your network is to always change your default usernames and passwords to strong, unique ones. And for employees who bring their own IOT devices into work, you can consider having a separate network for those devices.
Device Lifecycle Management
Updating your IoT devices regularly ensures that bugs and other security related issues are addressed promptly. Many IoT devices come with security patches that deal with the continuous new tactics of cyber criminals so always stay on top of the required security protocols.
Authentication
You may want to allow access to a particular device to specific users. An authentication for this may be to provide a username and password. There are of course other methods of authentication, such as digital signatures, pins, OTPs or access cards. These methods provide an extra layer of protection for your IoT devices.
Educate Your Employees and Security Policies
Your employees may not be aware that the IoT devices in the office are a potential security risk. Educate them on securing any IoT devices they bring into the office and what to do in case of a network breach.
Establishing security policies will increase security in the office. Informing employees of the best practices such as identifying and reporting suspicious emails, clicking suspicious links will create awareness about protecting your network in the office.
Always Be Prepared for Attacks
Hackers are innovative and always find ways to get into your IoT devices. The best way to counter this is to always be prepared for an attack. Detecting breaches and securing your network and devices ensures that you can cut off a hack before it gets any further.
Backing up your data guarantees that if your data is wiped, you can restore it and be back online in no time.
If you would like to use this infographic on your website, use the embed code below:
IoTs are a growing trend that started in the home and has now made its way into the workplace. It brings convenience, efficiency and productivity into the workplace amongst many other benefits.
However, businesses have to realise that manufacturers of IOT devices do not have security at the forefront of their mind. Thus, offices have to ensure that they have the best possible security protocols for their network and IoT devices and prevent the risks of future cyber attacks.

Valli is the Digital PR & SEO Manager at Market Inspector. She has an educational background in business management and marketing. She is a passionate digital marketer and enjoys building her skills within SEO, online marketing and PR. She holds over 5 years of experience in creating content, B2B marketing, link building and digital networking. Her focus lies in the areas of business, marketing, green energy and sustainability, to name a few. Her work has been published in various media such as Entrepreneur, Business Insider, Creativebloq, Designtaxi, and more.
We strive to connect our customers with the right product and supplier. Would you like to be part of Market Inspector?

